
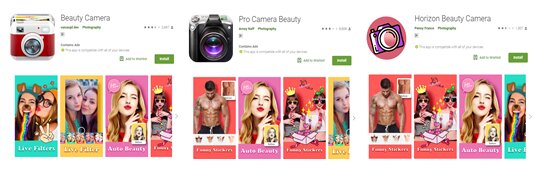
According to security researchers, several beauty camera apps on Google Play are capable of accessing remote ad configuration servers that can be used for malicious purposes. What’s not surprising is that some of these apps have millions of downloads given the popularity. A large number of the download counts originated from Asia, particularly in India.
A user can’t suspect any one of these apps immediately after downloading until after they decide to delete the app. These apps usually create a shortcut after being launched. However, it will hide its icon from the application list, making it more difficult for users to uninstall the app since it is hidden. Furthermore, these apps use packers to prevent them from being analyzed.
Not stopping there, these apps push several full-screen ads when users unlock their devices, including malicious ads (such as fraudulent content and pornography) that will pop up via the user’s browser. The analysis found that a paid pornography player detected as AndroidOS_PornPlayer.UHRXA that was downloaded when clicking the pop-up. None of these apps give any indication that they are the ones behind the ads, thus users might find it difficult to determine where they’re coming from.
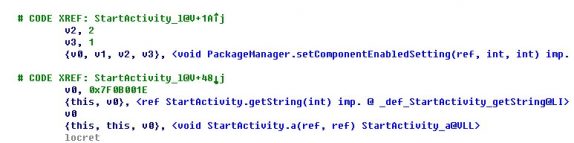
Some of these apps redirect to phishing websites that ask the user for personal information, such as addresses and phone numbers. The app will download an ad configuration from the remote servers and external URLs, which will analyze the target device to determine the advertisement’s behavior. The background service is then scheduled to parse the configuration and call the device browser.
Further investigation also led to another batch of photo filter-related apps that share similar behavior on Google Play. These apps seemingly allow users to “beautify” their pictures by uploading them to the designated server. However, instead of getting a final result with the edited photo, the user gets a picture with a fake update prompt in nine different languages. All the photos uploaded are collected by the apps and possibly use them for malicious purposes. However, Google has already taken down these apps.
