A new Android malware is affecting Android phone users in Ukraine by locking their mobile data. Called as Simplocker, the malware scans the device’s SD card or internal storage, encrypting any data files it finds there with a range of extensions, including obvious ones such as .jpg, .doc, .avi, and mp4. It then demands a ransom from them to recover their files.
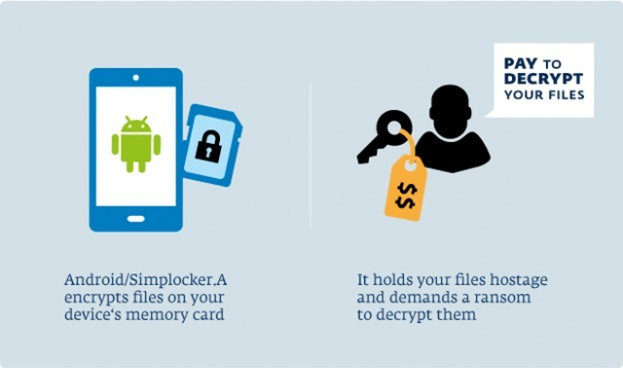
The ransom message is written in Russian, with payment demanded of 260 Ukrainian hryvnias. It’s the first malware found to be encrypting data on Android phones before demanding payment to decrypt it, according to a blog post by ESET’s security intelligence team lead Robert Lipovsky.
While the malware does contain functionality to decrypt the files, we strongly recommend against paying up – not only because that will only motivate other malware authors to continue these kinds of filthy operations, but also because there is no guarantee that the crook will keep their part of the deal and actually decrypt them, Lipovsky added.
The security firm touts that Simplocker is a cryptolocker style Android virus, which has an associated C&C server hosted on a TOR domain, scrambles files on the SD cards of infected devices before demanding payment to decrypt the files. It further stated that the malware’s prevalence is currently “very low” and is until now targeting Android users in Russian-speaking countries who downloading an app called ‘Sex xionix’ from a third-party app store. Simplocker is currently restricted to Ukraine and is not widespread.
