
Apple seems to be working on a new technology that could detect nuisance callers using spoofed phone numbers as the company filed for patents named “Detection of spoofed call information.” This system could let iPhones perform checks on a call to ascertain if it is genuine, if not warn the user of the nuisance callers or prevent it from disturbing the phone user at all.
There are cases where a call is made, a session initiation protocol (SIP) invite is sent along between phone networks to the user’s device. The SIP invite can contain a number of elements, with headers providing data meant to establish the call, such as speech codec information, network equipment identifiers, 3GPP VoLTE protocol information, server identifiers, and other elements.
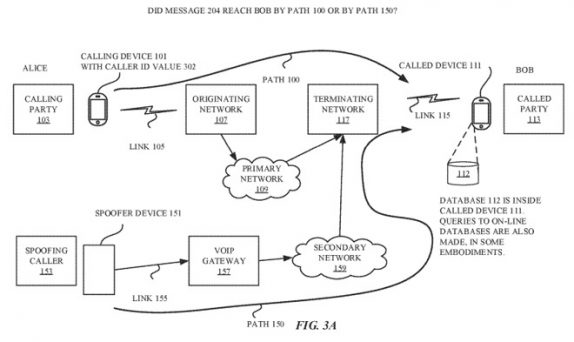
While the spoofing caller can fill in some SIP invite fields, some are populated or overwritten by network servers as it travels. This automatically added or altered information constitutes a signature for that network, which could be used to compare with other existing call signatures to determine if the call itself is legitimate.
The new Apple’s system could also be used to determine if the spoofer is passing the call through a forwarding device, which is connected to a legitimate network and sends the SIP invite itself, potentially through a number from the user’s address book. Using VIA headers, the device can check the number against the address book of the user, or a previously-established list, to verify the call is coming from the correct identified source.
In cases where the phone believes there to be too many discrepancies in the SIP invite, it can refer the “call record” to a database of other call records online. The database includes templates for different types of call initiation messages, which could be used to either confirm the call as legitimate or provide where it is really coming from.
Since Apple files many patent applications each week, it doesn’t mean the company would be utilizing it in reality and bring it in their products. Since it requires cooperation between telecommunications firms to set up and operate and Apple has influence over the mobile network, it could be used to implement the system in this way.
