
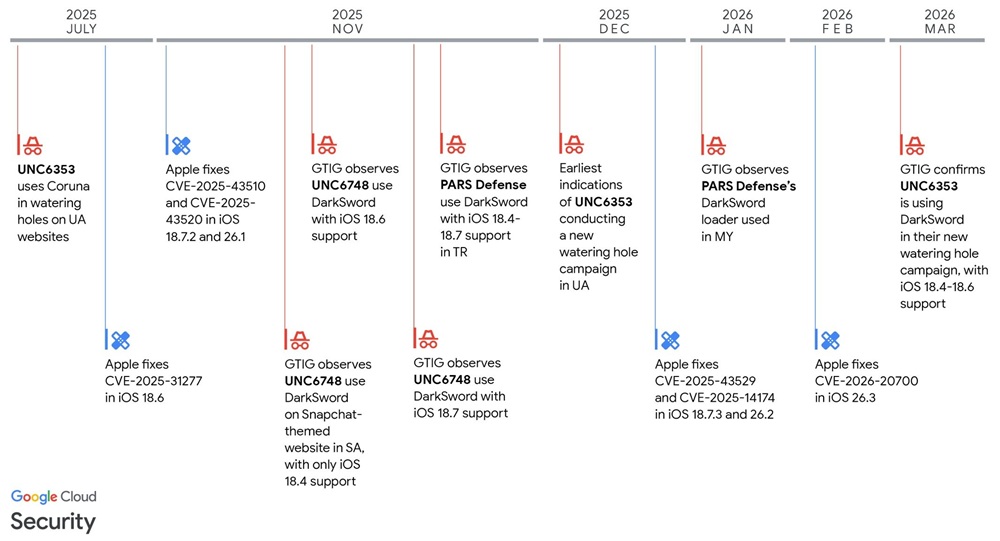
Google Threat Intelligence Group (GTIG), Lookout Threat Labs, and iVerify published coordinated research in March 2026 on DarkSword, a JavaScript-based full-chain exploit that compromises iOS devices running versions 18.4 through 18.7 (some variants limited to 18.4–18.6.2).
GTIG first observed DarkSword activity in November 2025, with use by multiple commercial surveillance vendors and suspected state-sponsored actors in campaigns targeting users in Saudi Arabia, Turkey, Malaysia, and Ukraine.
DarkSword chains six vulnerabilities to achieve remote code execution in Safari/WebKit, escape the WebContent and GPU sandboxes, pivot to mediaplaybackd, and obtain kernel read/write primitives for payload deployment. All stages and final payloads use pure JavaScript without Mach-O binaries.
Vulnerabilities in the Chain
The exploit uses the following vulnerabilities:
| Exploit Module | CVE | Description | Exploited as Zero-Day | Patched in iOS Version(s) |
|---|---|---|---|---|
| rce_module.js | CVE-2025-31277 | Memory corruption in JavaScriptCore | No | 18.6 |
| rce_worker_18.4.js | CVE-2026-20700 | User-mode PAC bypass in dyld | Yes | 26.3 |
| rce_worker_18.6.js / 18.7.js | CVE-2025-43529 | Memory corruption in JavaScriptCore | Yes | 18.7.3, 26.2 |
| rce_worker_18.6.js / 18.7.js | CVE-2026-20700 | User-mode PAC bypass in dyld | Yes | 26.3 |
| sbox0_main_18.4.js / sbx0_main.js | CVE-2025-14174 | Memory corruption in ANGLE | Yes | 18.7.3, 26.2 |
| sbx1_main.js | CVE-2025-43510 | Memory management vulnerability in iOS kernel | No | 18.7.2, 26.1 |
| pe_main.js | CVE-2025-43520 | Memory corruption vulnerability in iOS kernel | No | 18.7.2, 26.1 |
GTIG reported the vulnerabilities to Apple in late 2025. All are patched by iOS 26.3 (most earlier). Kernel fixes landed in 26.1, with RCEs in later releases. Devices on iOS 26.3.1 or 18.7.6 (at the time of publication) are not affected by observed variants.
Observed Campaigns
UNC6748 (early November 2025 onward):
Snapchat-themed site snapshare[.]chat targeting Saudi Arabia. Landing page uses uid sessionStorage check, obfuscation, anti-debugging, Chrome-to-Safari redirection via x-safari-https, and redirect to the legitimate Snapchat site. Loader initially fetches rce_worker_18.4.js, later adds 18.6 and 18.7 variants (with logic flaws in version handling). Uses the same sandbox escape/privilege escalation modules and GHOSTKNIFE payload.
PARS Defense (Turkish commercial surveillance vendor):
Late November 2025 in Turkey (iOS 18.4–18.7 support), January 2026 in Malaysia. Loader applies obfuscation and ECDH+AES encryption for exploit stages; fetches the correct RCE based on version. Additional fingerprinting and uid check in January variant. Redirects non-matching targets to legitimate sites. Payload: GHOSTSABER.
UNC6353 (suspected Russian espionage actor; previously used Coruna):
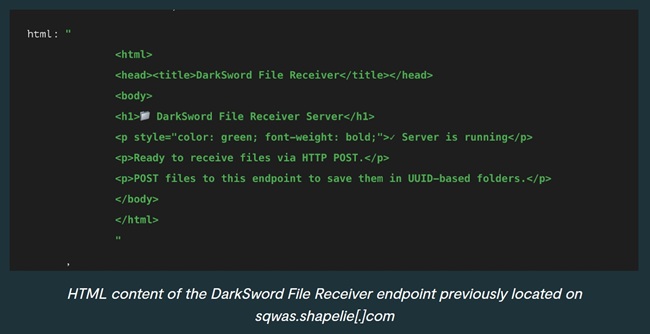
Watering-hole attacks on compromised Ukrainian sites (e.g., novosti.dn[.]ua, 7aac.gov[.]ua). Script tag loads from static.cdncounter[.]net; widgets.js creates an iframe to index.html (Russian comment: “если uid всё ещё нужен — просто устанавливаем”). Supports iOS 18.4–18.6 (correct version loading). Exfiltration to sqwas.shapelie[.]com (ports 8881/8882). Payload: GHOSTBLADE. Active at least December 2025–March 2026. GTIG collaborated with CERT-UA on mitigation.
Payloads
GHOSTBLADE (UNC6353):
JavaScript dataminer; collects iMessage/Telegram/WhatsApp data, call logs, contacts, device identifiers, keychains, SIM info, location history, Wi-Fi networks/passwords, photo metadata, iCloud Drive, Notes, Calendar, Health, Safari history/cookies/bookmarks, installed apps, crypto wallet data. Exfiltrates over HTTP/S. Deletes crash reports from /private/var/containers/Shared/SystemGroup/systemgroup.com.apple.osanalytics/DiagnosticReports/. Less capable than others; no continuous operation or modules. Debug logging and comments present.
GHOSTKNIFE (UNC6748):
JavaScript backdoor; exfiltrates signed-in accounts, messages, browser data, location history, recordings; supports file download, screenshots, and microphone audio. Custom binary protocol over HTTP with ECDH+AES encryption; config updates from C2. Writes to /tmp/<uuid>.<numbers>/ (STORAGE/DATA/TMP subfolders). Deletes crash logs (mediaplaybackd, SpringBoard, WebKit-related, panic-full-).
GHOSTSABER (PARS Defense):
JavaScript backdoor over HTTP/S; device/account enumeration, file listing, data exfiltration, arbitrary JS execution. Commands include ChangeStatusCheckSleepInterval, SendDeviceInfo, SendUserAccountsList, SendAppList, ExecuteSqliteQuery, SendThumbnails, SendApp, SendFiles, SendRegEx, SendFileList, EvalJs (some like SendCurrentLocation, SendScreenshot, RecordAudio reference send_command_to_upper_process but not implemented; possible follow-on binary).
All payloads stage/exfiltrate and then clean temporary files and crash logs (incomplete coverage in some cases). No long-term persistence observed.
Exploit Delivery and Loader
Delivery uses iframes, uid sessionStorage (set/check varies), and rce_loader.js fetching version-specific rce_worker_*.js and rce_module.js. Actors modified base logic (e.g., PARS encryption/fingerprinting, UNC6748 anti-debug/Chrome redirect, UNC6353 Russian comments). Loader manages Web Workers for RCE; 18.4 splits logic, 18.6/18.7 keeps it in the worker (placeholder in module).
- Sandbox escapes: CVE-2025-14174 (ANGLE OOB → GPU), CVE-2025-43510 (XNU COW → mediaplaybackd via XPC)
- Privilege escalation: CVE-2025-43520 (XNU VFS race); Libraries (Native, FileUtils, etc.) sourced from Webpack artifacts in GHOSTBLADE.
Outlook, Acknowledgments, and Recommendations
The use of DarkSword (and prior Coruna) demonstrates ongoing exploit proliferation across geography and motivation. A secondary market exists for sophisticated exploit chains, with groups customizing kits (possibly with LLM assistance).
Watering-hole attacks on legitimate sites approach zero-click; rapid exfiltration and cleanup help evade detection. These attacks bypass user training and OS data isolation, emphasizing the importance of rapid software updates and replacing older devices.
Acknowledgments: Research was coordinated among GTIG, Lookout, and iVerify, with GTIG and iVerify thanking Lookout, Google Project Zero, and Apple Security Engineering & Architecture for their support.
Indicators of Compromise (partial):
- Network:
snapshare[.]chat(UNC6748),static.cdncounter[.]net/cdncounter[.]net(UNC6353),sahibndn[.]io/e5.malaymoil[.]com(PARS),sqwas.shapelie[.]com(UNC6353 exfil, ports 8881/8882) - Files:
rce_loader.js,rce_module.js,rce_worker_18.4.js/18.6.js/18.7.js,sbx0_main_18.4.js,sbx1_main.js,pe_main.js - GHOSTBLADE SHA-256:
2e5a56beb63f21d9347310412ae6efb29fd3db2d3a3fc0798865a29a3c578d35 - Detection: Suspicious crashes (WebKit.WebContent/GPU, mediaplaybackd), unified logs (e.g., DarkSword-WIFI-DUMP tags), temporary files (
/tmp/keychain-2.db,wifi_passwords.txt, etc.)
Recommendations: Users should update to the latest iOS (≥26.3.1 / 18.7.6 at publication) and enable Lockdown Mode if updating is not possible. On iPhone 17, Memory Integrity Enforcement provides additional protection.
